Introduction
Cybersecurity is no longer a niche concern—it has become a daily operational risk for businesses, governments, and users alike. Attacks are increasing not just in number but also in sophistication, speed, and financial damage. One overlooked reason is scale: modern digital systems are deeply interconnected, so a single weakness can ripple across entire ecosystems. This reality makes major cybersecurity incident analysis essential, not optional, for anyone who relies on digital infrastructure.
The word “major” is often misused, but it carries real weight in security discussions. A major incident isn’t defined by headlines alone; it’s measured by scope, data sensitivity, downtime, and long-term trust erosion. These events don’t just disrupt systems—they alter business trajectories and regulatory scrutiny. In the middle of such chaos, major cybersecurity incident analysis becomes the only reliable way to understand what actually failed versus what was merely exposed.
This article does not chase breaking news or recycle breach announcements. Its scope is analytical and forward-looking, focusing on how large-scale incidents unfold, why they repeat, and what they reveal about modern security blind spots. The goal is clarity, not fear—understanding patterns rather than reacting to noise.
What Is a Major Cybersecurity Incident?
A serious security event is not defined by drama but by consequence. A major incident occurs when unauthorized access, system disruption, or data compromise crosses a threshold that materially affects operations, users, or legal standing. Major Cybersecurity Incident Analysis helps separate meaningful failures from routine security noise by focusing on impact rather than intent.
Smaller incidents tend to be isolated and recoverable with minimal disruption. A major cybersecurity breach, by contrast, often involves multiple systems, delayed detection, and sensitive data exposure. The difference lies in scale, persistence, and the inability of existing controls to contain the damage quickly. Midway through any major cybersecurity incident analysis, a clear pattern emerges: major incidents expose systemic weaknesses rather than single mistakes.
In real-world terms, these incidents influence stock prices, trigger government investigations, and permanently damage brand credibility. They are not technical footnotes; they are business events with security roots. Understanding what qualifies as “major” is the first step toward building defenses that account for real risk instead of theoretical threats.

Timeline of a Typical Major Cybersecurity Incident
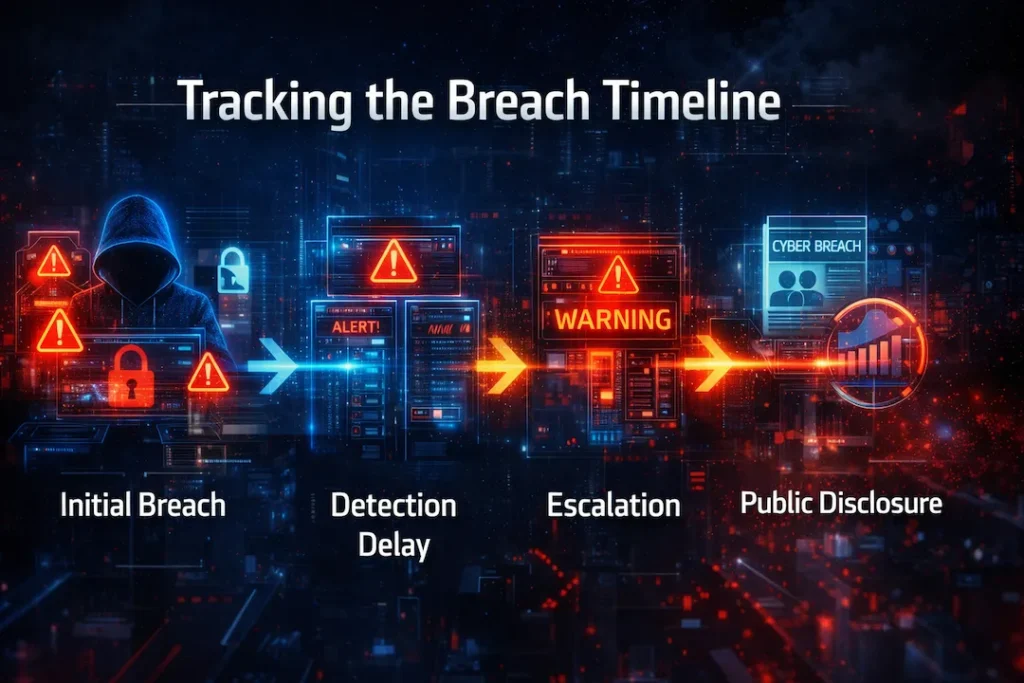
Every large-scale breach follows a predictable rhythm, even if the details differ. The process usually begins quietly, with attackers exploiting a small opening that appears harmless at first. Major Cybersecurity Incident Analysis shows that the most dangerous breaches often start without alarms, alerts, or obvious system failures.
Detection rarely happens immediately. Weeks or even months may pass before abnormal behavior is noticed, often by external researchers rather than internal teams. This delay allows attackers to deepen access, extract data, and prepare exit strategies. At the midpoint of a major cybersecurity incident analysis, delayed detection consistently appears as a multiplier of damage rather than a secondary issue.
Escalation follows once the breach becomes undeniable. Internal teams scramble to isolate systems while leadership manages public and legal pressure. Public disclosure usually comes last, shaped as much by regulatory timelines as by technical readiness. By the time users are informed, the real damage has often already occurred behind the scenes.
Common Causes Behind Major Cybersecurity Breaches
Large breaches are rarely caused by exotic exploits; they thrive on basic failures repeated at scale. Major Cybersecurity Incident Analysis reveals that most incidents trace back to preventable weaknesses rather than advanced attacker genius. Understanding cybersecurity breach causes requires examining both technology and behavior.
Weak authentication remains a primary entry point. Password reuse, lack of multi-factor authentication, and poorly managed credentials give attackers quiet access without triggering alarms. Once inside, unpatched systems provide an easy path forward. Known vulnerabilities often remain exposed for months, creating predictable targets that attackers actively scan for.
Insider threats complicate detection because access already exists. Whether malicious or accidental, internal misuse bypasses many perimeter defenses. Phishing and social engineering bridge the technical-human gap, tricking employees into granting access voluntarily. Cloud misconfigurations amplify all these risks by exposing sensitive resources directly to the internet. In the middle of any major cybersecurity incident analysis, these causes appear less as anomalies and more as recurring patterns organizations fail to correct.
Technical Analysis of Major Cybersecurity Incidents
Attackers don’t rely on a single method; they chain techniques together with strategic precision. Major Cybersecurity Incident Analysis breaks down these attack vectors to show how initial access turns into full compromise. The process often begins with credential theft or exploit abuse, not brute force attacks.
Malware and ransomware act as tools rather than goals. They establish persistence, encrypt assets, or quietly extract data while masking activity as legitimate traffic. Zero-day exploits are rarer but devastating, especially when combined with delayed patch cycles. Midway through a major cybersecurity incident analysis, lateral movement becomes the defining factor—attackers hop between systems using trust relationships rather than exploits.
This internal spread is what transforms a contained breach into an enterprise-wide crisis. Shared credentials, flat networks, and excessive permissions accelerate the damage. Technical failure alone doesn’t explain the outcome; architectural decisions do. Understanding this movement is critical to designing systems that fail safely instead of catastrophically.
Impact Analysis of Major Cybersecurity Incidents
The damage from a breach extends far beyond IT budgets. Major cybersecurity incident analysis consistently shows that financial losses include remediation costs, downtime, lost contracts, and long-term revenue decline. These expenses often exceed initial estimates by multiples.
User data exposure creates irreversible harm. Once personal or proprietary information is leaked, control is permanently lost, regardless of public assurances. Brand trust damage follows quickly, as customers reassess whether security claims align with reality. In the center of any major cybersecurity incident analysis, reputation emerges as the most fragile asset—hard to build and easy to destroy.
Legal and regulatory consequences add another layer of pressure. Compliance failures invite fines, audits, and lawsuits that extend for years. The impact of cybersecurity incidents is cumulative, not isolated, reshaping how organizations operate long after systems are restored. The true cost is measured in credibility as much as currency.
Case Study Style Breakdown (Generic, Not News Copy)
Imagine a global tech company with millions of users and a cloud-first infrastructure. The breach begins through a misconfigured development environment left exposed during rapid deployment. Major cybersecurity incident analysis would immediately flag speed-over-security as the root issue, not the attacker’s sophistication.
Once inside, attackers leverage shared credentials to access production systems. Monitoring tools fail to detect anomalies because activity appears legitimate. Data exfiltration continues quietly until a third-party researcher reports leaked information online. Midway through the Major Cybersecurity Incident Analysis, it becomes clear that detection failure mattered more than the initial breach.
What should have been done is equally revealing. Segmented access, continuous audits, and enforced least-privilege policies would have limited the spread. The incident wasn’t inevitable—it was enabled by convenience-driven decisions that prioritized growth over resilience.

Lessons Learned from Major Cybersecurity Incidents
Organizations tend to ignore warnings until consequences become unavoidable. Major Cybersecurity Incident Analysis shows that known risks are often documented internally but deprioritized due to cost, time, or complacency. This pattern repeats across industries.
Human error is frequently blamed, but system design enables that error. Overreliance on employees to compensate for weak controls creates fragile defenses. In the middle of any major cybersecurity incident analysis, the “we are secure enough” mindset stands out as the most dangerous vulnerability of all.
Security is not a static achievement; it is a continuous process that degrades without attention. Treating security as a checklist item rather than an operational discipline guarantees future incidents. The lesson is simple but uncomfortable: ignoring small risks today creates major failures tomorrow.
How Organizations Can Prevent Major Cybersecurity Incidents
Prevention is less about tools and more about discipline. Major Cybersecurity Incident Analysis highlights that regular security audits uncover issues long before attackers do. These audits must test real-world scenarios, not theoretical compliance.
Zero trust models reduce damage by assuming breach rather than preventing it entirely. Limiting access by default slows lateral movement and buys critical response time. Employee training addresses phishing and social engineering, but only when paired with enforceable controls. In the center of effective Major Cybersecurity Incident Analysis, preparation always outperforms reaction.
Incident response planning turns chaos into coordination. Clear roles, rehearsed procedures, and rapid decision-making reduce confusion when breaches occur. Cybersecurity incident response is not about perfection—it’s about reducing impact when failure inevitably happens.
Future of Cybersecurity Incident Management
Automation is reshaping how incidents are detected and contained. Major Cybersecurity Incident Analysis increasingly points to AI-driven monitoring as a force multiplier rather than a replacement for human judgment. These systems identify anomalies faster than manual review ever could.
Automated detection shortens response time, but attackers adapt just as quickly. They study defensive models and adjust behavior to blend in. In the middle of future-focused Major Cybersecurity Incident Analysis, adaptability emerges as the defining trait on both sides.
The arms race will continue, but advantage favors those who learn faster. Security strategies that evolve with threats will define resilience in the next decade.

Frequently Asked Questions (FAQ)
What makes an incident qualify for Major Cybersecurity Incident Analysis?
A cybersecurity event becomes “major” when its impact extends beyond a single system or short-term disruption. Major Cybersecurity Incident Analysis focuses on incidents involving large-scale data exposure, prolonged downtime, regulatory consequences, or widespread loss of user trust. Severity is measured by business impact, not by how sophisticated the attack sounds.
How is Major Cybersecurity Incident Analysis different from basic breach reporting?
Breach reporting tells you what happened; Major Cybersecurity Incident Analysis explains why it happened and how it escalated. It examines root causes, detection failures, internal weaknesses, and response gaps rather than just listing leaked data or affected users.
Why do major cybersecurity breaches often go undetected for months?
Most major cybersecurity breaches blend into normal system activity. Attackers exploit trusted credentials, weak monitoring, and alert fatigue. In many Major Cybersecurity Incident Analysis cases, detection occurs only after external disclosure, not internal discovery—highlighting visibility gaps rather than lack of tools.
Are major cybersecurity incidents always caused by advanced hackers?
No. The majority of incidents analyzed through Major Cybersecurity Incident Analysis originate from basic failures such as unpatched systems, weak authentication, or misconfigured cloud services. Advanced techniques amplify damage, but simple mistakes usually open the door.
What role does human error play in major cybersecurity incidents?
Human error is a factor, but rarely the root cause. Major Cybersecurity Incident Analysis consistently shows that poor system design, excessive permissions, and lack of safeguards allow small human mistakes to become large-scale breaches.
Can strong cybersecurity tools alone prevent major incidents?
Tools help, but they don’t prevent complacency. Major Cybersecurity Incident Analysis proves that organizations with expensive security stacks still suffer breaches due to weak processes, ignored alerts, or poor incident response planning. Discipline matters more than tool count.
Final Thoughts
Security failures rarely come without warning; they come without attention. Major Cybersecurity Incident Analysis provides the lens needed to see patterns instead of isolated events. Awareness, preparation, and disciplined execution remain the most reliable defenses.
Organizations that treat security as strategy—not expense—will absorb shocks without collapse. Those that don’t will eventually become case studies themselves.


5 thoughts on “Major Cybersecurity Incident Analysis: Causes, Impact, and Lessons for the Future”
Comments are closed.