Focus Keyword: Zero Trust Cloud Security | Secondary Keywords: zero trust architecture, cloud security model, identity and access management, least privilege access, micro-segmentation, multi-cloud security | LSI Keywords: cloud data breach prevention, network segmentation, continuous authentication, lateral movement attacks, cloud workload security
Zero Trust Cloud Security has become a necessity for US businesses operating in today’s distributed cloud environments. Your cloud infrastructure is only as secure as the assumptions you make about who and what can be trusted — and most breaches happen because of misplaced trust. According to IBM’s Cost of a Data Breach Report, the average breach in the US now costs over $4.4 million, and CISA reports that credential-based attacks account for the majority of cloud intrusions. That risk is real, it’s growing, and it’s hitting US businesses of every size.
The old security model — keep threats outside the network and trust everything inside — is broken. Zero Trust Cloud Security flips that entirely. It demands verification at every step: every user, every device, every request, every time. This article breaks down what zero trust architecture is, how it works in cloud environments, and why it has become the security standard modern US businesses can’t afford to ignore.
What Is Zero Trust Cloud Security?
Zero Trust Cloud Security is a security framework built on one rule: trust nothing, verify everything. It eliminates the idea of a “safe inside” zone by treating every access request as potentially hostile — whether it originates inside your office or from the other side of the world.
This matters enormously for cloud environments, where data, applications, and users are spread across multiple locations and providers. The old perimeter-based model simply doesn’t hold when your infrastructure has no clear boundary.
Zero Trust Architecture Explained Simply — A Core Concept in Zero Trust Cloud Security
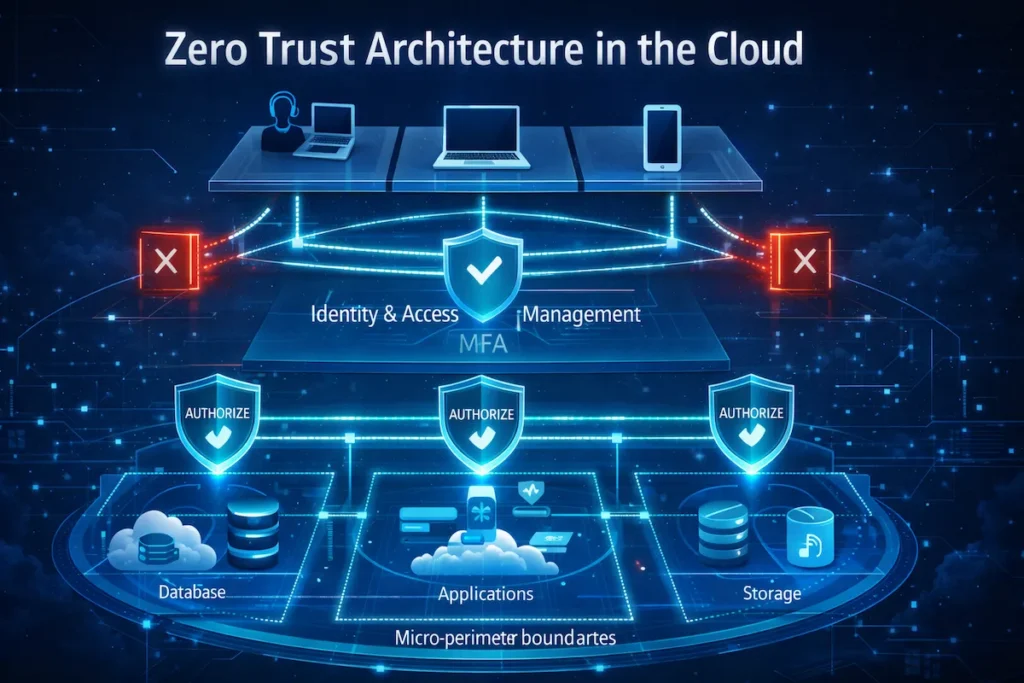
Zero Trust Architecture (ZTA) is the structural backbone of Zero Trust Cloud Security. At its core, it means no user, device, or system is automatically trusted — even after logging in once. Every session is continuously re-evaluated.
Think of it this way: instead of a hotel where your key card opens every room on your floor, zero trust gives you a unique key for each room — and verifies your identity again every time you open a new door. Access is always contextual, always limited, and always logged.
ZTA operates through three interconnected layers: identity verification, device health checks, and access policy enforcement. Together, they ensure that even if one account is compromised, an attacker cannot move freely through your cloud environment. If you’re weighing cloud architecture decisions that affect how zero trust fits your setup, this guide to hybrid cloud vs public cloud is worth reviewing before you build your security framework.
Why Traditional Cloud Security Models Fail — And Why Zero Trust Cloud Security Is the Answer
Traditional security relied on perimeter-based defense — build a strong wall around your network and assume everything inside is safe. That approach worked reasonably well when employees sat in one office and data lived in one data center.
Today, it’s a liability. Remote workers log in from coffee shops. Applications run across AWS, Azure, and Google Cloud simultaneously. Third-party vendors access your systems through APIs. There is no single perimeter left to protect.
Traditional models fail because they create implicit trust. Once inside, users often hold far more access than they need. Attackers who breach a single account can move laterally across systems for weeks before detection. Zero Trust Cloud Security exists specifically to close that gap — and if you want a broader look at where businesses typically go wrong, this breakdown of top cloud security mistakes companies still make covers the most common and costly missteps.
Core Principles of Zero Trust Cloud Security
Zero Trust Cloud Security isn’t a product you install. It’s a strategy built on core principles that fundamentally reshape how access and authentication work across your cloud environment.
Never Trust, Always Verify—The Foundation of Zero Trust Cloud Security
This is the defining principle of Zero Trust Cloud Security: no entity — user, device, application, or service — is trusted by default. Every access request must be authenticated and authorized before it’s granted, regardless of where it originates.
In a cloud context, this means even an employee on a company-issued laptop inside your corporate network still needs to verify identity and meet policy requirements before reaching sensitive data. A valid VPN connection or internal IP address is not enough.
“Never trust, always verify” transforms your cloud from a place where attackers can hide to an environment where every action is accountable.
Least Privilege Access—Minimizing Risk in Zero Trust Cloud Security
Least privilege means giving users and systems only the access they need for their specific role — nothing more. Under Zero Trust Cloud Security, this is enforced at a granular level across every cloud resource.
If a developer needs to push code to a staging environment, they shouldn’t also have read access to production databases. If an application writes to one S3 bucket, it shouldn’t have permissions across your entire storage layer. Limiting access scope directly limits the damage when credentials are stolen or misused.
Many US businesses that have dealt with insider threats or compromised accounts found that excessive permissions turned a contained incident into a catastrophic breach. Least privilege is the most direct answer to that exposure.
Continuous Authentication & Authorization—How Zero Trust Cloud Security Stays Current
Zero Trust Cloud Security doesn’t just verify identity at login. It continuously monitors sessions, re-evaluating access based on behavior, device health, location, and real-time risk signals.
If a user suddenly downloads large volumes of data at 2 AM from an unrecognized location, Zero Trust systems flag it immediately and can automatically revoke access or trigger re-authentication. This posture is something static security models are structurally incapable of matching.
Modern implementations use AI and machine learning to establish behavioral baselines and detect deviations in real time — making continuous authorization both scalable and practical for enterprise cloud environments.
How Zero Trust Cloud Security Strengthens Cloud Environments
Zero Trust Cloud Security solves specific, real-world problems that cloud teams deal with daily. Here’s where it delivers the most impact.
Protection Against Cloud Data Breaches—Zero Trust Cloud Security in Action
Cloud data breaches almost always begin with a single compromised credential. Under a traditional model, that one credential becomes a master key to dozens of systems. Zero Trust Cloud Security removes that risk by segmenting access so tightly that a stolen password opens only one door.
IBM’s breach data puts the average US cost at over $4.4 million per incident, with misconfigured cloud resources and over-privileged accounts responsible for a significant share of those breaches — both problems zero trust directly addresses. For a deeper look at how to protect sensitive data across environments, this guide on securing data in multi-cloud environments is directly relevant.
By combining multi-factor authentication, just-in-time access provisioning, and continuous monitoring, Zero Trust Cloud Security ensures that even a successful phishing attack causes limited damage.
Securing Remote Work & Multi-Cloud Access—Why Zero Trust Cloud Security Scales
Remote work is permanent infrastructure now, and so is multi-cloud. US enterprises routinely run workloads across two or more cloud providers while supporting thousands of remote employees. This creates an access surface that traditional perimeter security simply cannot manage.
Zero Trust Cloud Security scales naturally to this reality. Because it’s identity-centric rather than network-centric, it doesn’t matter where a user sits or which cloud holds the data. The same verification and policy framework applies everywhere, consistently.
This is a primary reason why companies with distributed teams — from tech startups in Austin to financial institutions in New York — are moving to zero trust as their core cloud security model. The zero trust framework also pairs well with strong foundational practices covered in these cloud security tips for protecting your data online.
Preventing Lateral Movement Attacks—A Critical Win for Zero Trust Cloud Security
Lateral movement is how attackers turn initial access into full-scale breaches — escalating privileges and reaching more sensitive systems over time. It’s the technique behind most major enterprise compromises.
Zero Trust Cloud Security fights lateral movement through micro-segmentation — dividing your cloud environment into small, isolated zones where moving between zones requires its own verification. Even if an attacker compromises one workload, they hit a wall at every boundary.
This capability is especially valuable for enterprises running complex cloud architectures where east-west traffic (movement between internal systems) is often completely unmonitored in traditional setups.

Zero Trust Cloud Security vs Traditional Cloud Security
| Aspect | Traditional Security Model | Zero Trust Cloud Security |
|---|---|---|
| Trust assumption | Trusts internal network by default | Trusts nothing by default |
| Authentication | One-time authentication at login | Continuous, session-by-session authentication |
| Network access | Flat, broad access after entry | Micro-segmented, need-based access |
| Security focus | Perimeter-focused security | Identity-focused security |
| Visibility | Limited insight into east-west traffic | Full access logging and continuous monitoring |
| Remote work fit | Poor — relies on VPN chokepoints | Strong — consistent security across all locations |
Perimeter-Based Security Limitations—What Zero Trust Cloud Security Replaces
Perimeter-based security assumes a clear inside and outside. The firewall is the wall; everything inside is trusted. That worked for on-premises infrastructure with predictable traffic.
In the cloud, that perimeter is gone. Data moves constantly between SaaS apps, cloud storage, APIs, and remote endpoints. Traditional VPNs and firewalls create a false sense of security — and a single, predictable choke point that experienced attackers know exactly how to exploit.
The limitations are concrete: no visibility into east-west traffic, flat network access after initial authentication, and no mechanism to enforce dynamic access policies based on behavior or device health.
Zero Trust Security Advantages in the Cloud—Why the Shift Is Worth It
Zero Trust Cloud Security is built for the way modern infrastructure actually works — distributed, dynamic, and identity-driven. Granular access control ensures users and systems only reach what they need. Continuous verification catches compromised credentials before major damage is done. Full logging across all access requests means nothing moves undetected. And application-level policy enforcement means security travels with your data, wherever it lives.
Traditional security protects the building. Zero Trust Cloud Security protects every room inside it — and re-checks credentials at every door.
Implementing Zero Trust Cloud Security Step-by-Step
Zero Trust Cloud Security is a gradual process, not a one-day migration. Here’s a practical roadmap US IT teams can follow to build a strong foundation without disrupting operations.
Identity & Access Management (IAM)—The Starting Point for Zero Trust Cloud Security
IAM is the cornerstone of any Zero Trust Cloud Security implementation. Before enforcing least privilege or continuous verification, you need a clear, current picture of who and what is accessing your cloud environment.
Start by auditing all user accounts, service accounts, and API keys. Remove dormant accounts and over-privileged roles immediately. Then enforce multi-factor authentication (MFA) across all cloud access points — this single step stops the vast majority of credential-based attacks.
Integrate a modern identity provider — Okta, Azure Active Directory, or AWS IAM Identity Center — that supports conditional access policies, SSO, and real-time risk scoring. This establishes the identity layer zero trust requires.
Network Segmentation & Micro-Perimeters—Structuring Zero Trust Cloud Security
Once identity is solid, focus on network architecture. Zero Trust Cloud Security uses micro-segmentation to divide your cloud environment into isolated zones, each governed by its own access policies.
Your customer database doesn’t share a flat network with internal analytics tools. Your CI/CD pipeline is isolated from production systems. Each zone controls its own ingress and egress, and cross-zone traffic requires explicit authorization.
Tools like AWS Security Groups, Azure Virtual Networks, Illumio, and Zscaler make micro-segmentation achievable even in complex multi-cloud setups. Pairing micro-segmentation with strong encryption at the storage layer is equally important — this resource on advanced encryption techniques for cloud storage covers exactly that.
Continuous Monitoring & AI-Driven Analytics—Sustaining Zero Trust Cloud Security
Zero Trust Cloud Security demands ongoing visibility. You can’t enforce a model you can’t see. Continuous monitoring gives you real-time insight into every access request, session, and data movement across your environment.
Deploy a SIEM platform — Microsoft Sentinel, AWS Security Hub, or a comparable solution — to aggregate and analyze logs at scale. Pair it with user and entity behavior analytics (UEBA) to catch anomalies that rule-based systems miss entirely.
AI-driven analytics establish behavioral baselines for users and workloads, then flag deviations automatically. This makes continuous monitoring practical even for lean security teams managing large cloud footprints.

Common Mistakes When Adopting Zero Trust Cloud Security
Many organizations invest in zero trust tools and still end up with significant gaps. These mistakes are avoidable—if you know what to look for.
Treating Zero Trust as a Tool, Not a Strategy—A Costly Misconception in Zero Trust Cloud Security
Zero trust is not a product. You cannot buy a “zero trust appliance” and declare the work done. Yet many IT teams treat a single tool purchase—an MFA solution, a CASB product, a new firewall—as a complete zero trust implementation.
Zero Trust Cloud Security is a strategic framework that spans identity, network architecture, access policies, monitoring, and incident response. It requires genuine alignment across IT, security, DevOps, and leadership. Without that alignment, individual tools produce security theater rather than real protection.
Start with a strategy document. Map your assets, define your protect surfaces, and build a phased roadmap before committing to any new tooling.
Ignoring Legacy Cloud Workloads—A Hidden Gap in Zero Trust Cloud Security
Most US enterprises run a mix of cloud-native applications and older workloads that were lifted and shifted to the cloud without security modernization. These legacy systems often can’t support modern authentication protocols, resist easy segmentation, and lack adequate logging.
Ignoring them creates a visible blind spot in your Zero Trust Cloud Security posture. Attackers actively target legacy environments because they know controls there are weaker.
Address legacy workloads by categorizing them, applying compensating controls—API gateways, network-level access restrictions—and building a realistic modernization roadmap. Don’t let perfect be the enemy of progress.
Benefits and Challenges of Zero Trust Cloud Security
Zero trust delivers real, measurable value. But it also comes with genuine implementation complexity. Here’s an honest assessment of both.
Key Benefits for Modern Cloud Infrastructure—The Case for Zero Trust Cloud Security
The security gains from Zero Trust Cloud Security are well-documented. Reduced breach risk comes from limiting lateral movement and enforcing least privilege. Faster incident response comes from continuous monitoring that surfaces threats earlier. Stronger compliance posture comes from granular access logging and access controls that support HIPAA Security Rule requirements and broader regulatory frameworks common in US industries.
Organizations processing payments must align with PCI DSS standards to protect cardholder data.
Many SaaS providers pursue SOC 2 reporting to demonstrate mature access control and monitoring practices.
Beyond security, zero trust improves operational visibility. IT teams get auditable records of who accessed what and when—something traditional architectures rarely produce cleanly. This matters for internal reviews and external audits alike.
Remote workforce enablement is a practical bonus. With Zero Trust Cloud Security, access policies are consistent whether an employee is in-office, remote, or traveling—without the complexity and latency of legacy VPN infrastructure.
Real Challenges Businesses Must Prepare For—Honest Realities of Zero Trust Cloud Security
Implementation complexity is the primary challenge. Zero Trust Cloud Security requires simultaneous changes to identity systems, network architecture, application integrations, and monitoring tooling. For large, established environments, this is realistically a multi-year journey.
Cost is a genuine consideration. Modern IAM platforms, SIEM solutions, and micro-segmentation tools represent real budget commitments. Smaller US businesses should prioritize the highest-risk areas first and build incrementally.
User friction is also a risk if policies aren’t tuned carefully. Strict access controls can slow workflows when applied bluntly. Adaptive authentication—which reduces friction for low-risk, recognized sessions—helps balance security and usability.
Is Zero Trust Cloud Security Worth It for Businesses?
The answer is yes—but the right approach depends on your size, risk profile, and cloud maturity.
Best Use Cases by Business Size—Zero Trust Cloud Security for Every Stage
For small and mid-size US businesses, Zero Trust Cloud Security starts with three moves that cost relatively little: enforce MFA on all cloud accounts, implement role-based access controls with least privilege, and enable cloud-native logging. These deliver meaningful protection without requiring enterprise budgets.
Mid-market companies with expanding cloud footprints should add identity provider integration, micro-segmentation for critical workloads, and UEBA to detect insider threats. A phased roadmap becomes essential at this stage.
Large enterprises with complex multi-cloud environments benefit most from full implementations—mature IAM, AI-driven monitoring, service mesh security for microservices, and automated policy enforcement. The upfront investment returns through reduced breach costs and improved audit outcomes.
Future of Cloud Security with Zero Trust—Where Zero Trust Cloud Security Is Heading
Zero Trust Cloud Security is already the dominant framework shaping cloud security’s evolution. The US federal government’s adoption of zero trust as a mandatory standard—through CISA’s Zero Trust Maturity Model and Executive Order 14028—reflects how seriously the broader security community views this direction.
Going forward, zero trust principles will be embedded more deeply into cloud platforms themselves. AI-driven policy automation will reduce manual configuration burdens. Identity will extend to non-human entities—APIs, microservices, IoT devices—expanding zero trust coverage across the full attack surface.
Businesses building zero trust foundations today will adapt more easily as these capabilities mature, rather than scrambling to retrofit security after the next generation of cloud threats arrives.

Frequently Asked Questions About Zero Trust Cloud Security
Q: Is Zero Trust Cloud Security only for large enterprises?
No. While large enterprises benefit most from full implementations, businesses of any size can apply zero trust principles. Starting with MFA enforcement, least privilege access, and cloud-native logging delivers meaningful protection even for small teams with limited budgets.
Q: How long does it take to implement Zero Trust Cloud Security?
It depends on your environment’s complexity. A focused SMB can implement foundational zero trust controls in weeks. A large enterprise with legacy systems and multi-cloud infrastructure should plan for a phased rollout over one to three years.
Q: Does Zero Trust Cloud Security replace a VPN?
Not immediately — but in many cases it eventually can. Zero trust frameworks, especially when combined with ZTNA (Zero Trust Network Access) solutions, provide more granular and scalable access control than traditional VPNs, without the performance bottlenecks.
Q: What’s the first step to adopting Zero Trust Cloud Security?
Start with identity. Audit your current accounts and permissions, enforce MFA everywhere, and integrate a modern identity provider. Identity is the foundation everything else in zero trust is built on.
Q: Can Zero Trust Cloud Security work alongside existing security tools we already have?
Yes. Zero Trust Cloud Security is designed to integrate with your existing stack, not replace everything overnight. Your current firewalls, endpoint protection, and SIEM tools can all operate within a zero trust framework. The strategy layers on top of what you have, gradually tightening access controls and adding continuous verification without requiring you to scrap your current investments.
Q: How does Zero Trust Cloud Security help with regulatory compliance in the US?
Zero trust directly supports compliance with major US regulatory frameworks including HIPAA, PCI-DSS, SOC 2, and CMMC. Because every access request is logged, verified, and tied to a specific identity, you automatically generate the audit trails these frameworks require. Least privilege enforcement also satisfies the “minimum necessary access” requirements found in HIPAA and similar standards — making compliance audits significantly less painful.
Q: What is the biggest security risk for businesses that delay adopting Zero Trust Cloud Security?
The biggest risk is undetected lateral movement. When a business continues running on implicit trust — where authenticated users have broad, unchecked access — a single compromised credential can give an attacker weeks of undetected access across your cloud environment. Most major breaches in the US didn’t happen because attackers broke through a wall. They happened because once inside, nothing stopped them from moving freely. Zero trust removes that free pass entirely.
Final Thoughts on Zero Trust Cloud Security
Zero Trust Cloud Security isn’t a trend — it’s a direct response to how infrastructure operates and how attacks happen today. The assumption that anything inside your network is automatically safe has been invalidated by cloud adoption, remote work, and attacks that grow more sophisticated every year.
The core message is clear: verify everything, limit access to what’s necessary, and monitor continuously. Applied consistently, these principles reduce your attack surface significantly and contain the damage when — not if — a credential is eventually compromised.
For US businesses at any stage, the path forward starts with understanding your current access posture, identifying your highest-risk assets, and committing to a realistic zero trust roadmap. You don’t need to do everything at once. But you do need to start.
Zero Trust Cloud Security is the most practical answer to the most pressing cloud security problem: you cannot secure what you implicitly trust.
Start with identity. Build from there. And treat zero trust not as a destination you reach once, but as a practice you sustain — because your cloud environment, your threats, and your business never stop changing.

